BleepingComputer
By Ionut Ilascu – 9/17/2019
Small to mid-sized businesses can keep safe from most cyber attacks by protecting the ports that threat actors target the most. Three of them stand out in a crowd of more than 130,000 targeted in cyber incidents.
A report from threat intelligence and defense company Alert Logic enumerates the top weaknesses observed in attacks against over 4,000 of its customers.
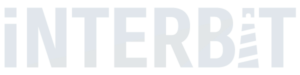
Top TCP ports attacked
According to the report, the ports most frequently used to carry out an attack are 22, 80, and 443, which correspond to SSH (Secure Shell), the HTTP (Hypertext Transfer Protocol), and the HTTPS (Hypertext Transfer Protocol Secure).
Alert Logic says that these appear in 65% of the incidents, and it makes sense since they need to be open for communication, be it secured or plain text.
Coming in fourth place is the port for Microsoft’s Remote Desktop Protocol (RDP), responsible for remote communication between machines. RDP attracted attention this year through multiple patches for vulnerabilities leading to remote code execution (CVE-2019-1181, CVE-2019-1182, and CVE-2019-0708).
“As basic guidance, security across all network ports should include defense-in-depth. Ports that are not in use should be closed and organizations should install a firewall on every host as well as monitor and filter port traffic. Regular port scans and penetration testing are also best practices to help ensure there are no unchecked vulnerabilities” – Alert Logic
A port tagged as a serious risk is for the File Transfer Protocol (FTP – 20, 21). Active servers were found on printers, cameras, and uninterruptible power supplies, which are estimated to be up to a third of all the FTP servers discovered.
The company’s recommendation to reduce potential risk from these ports is to maintain up-to-date and harden devices, software or services that rely on these ports in order to close attack avenues.
Running ancient software
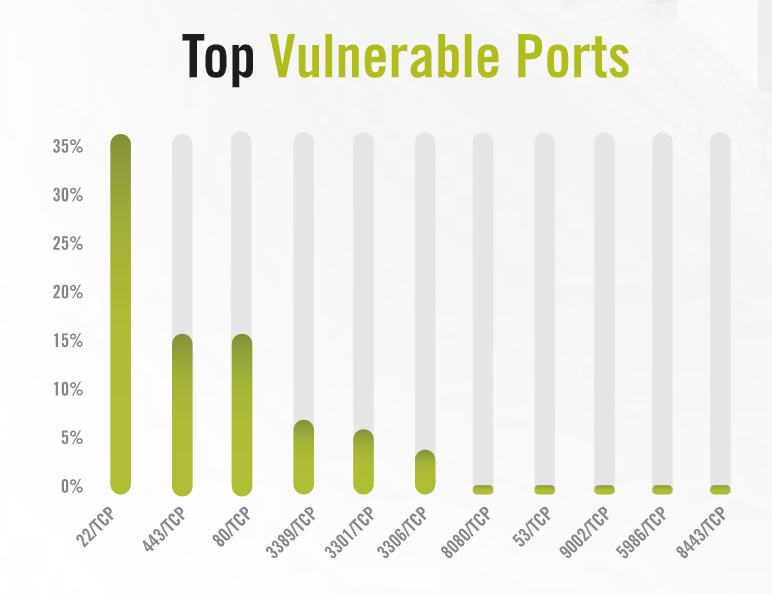
Additional vulnerabilities undermining the security of an organization refer to weak encryption and outdated software, which accounted for 66% and 75%, respectively, of the issues Alert Logic noticed with its customers.
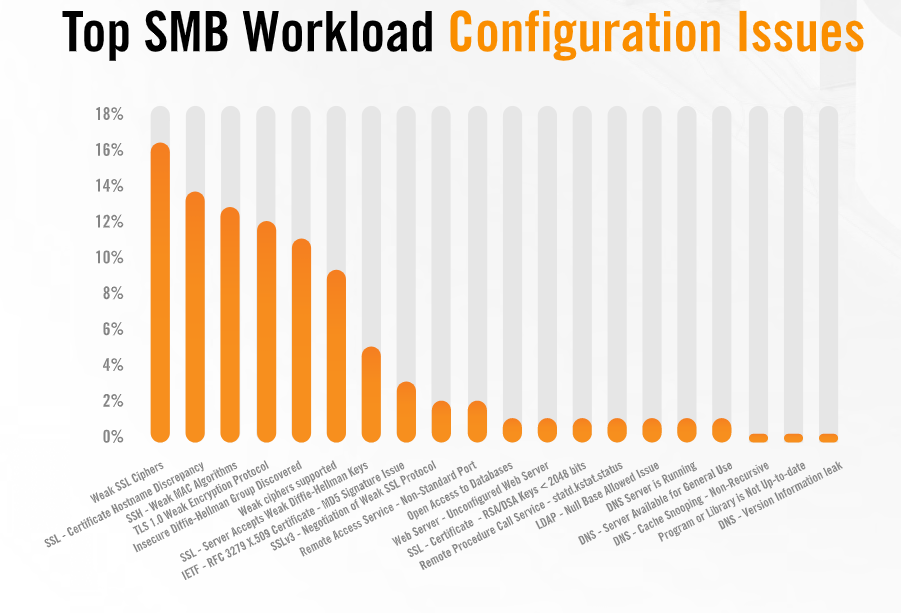
The problems keep on piling as the company found that over 66% of the scanned hosts run Windows 7, an operating system (OS) that will no longer benefit from support past January 14, 2020. At the opposite end, Windows Server 2019 is barely seen on SMBs infrastructure.
For some reason, Windows XP, which had its final release in 2008 and reached end of support in 2014, continues to be present in a “non-trivial number.”
Alert Logic says that it even found Windows NT systems (released in 1993) on its customers’ network. The risk with running them is that it would make an attacker’s lateral movement dead easy.
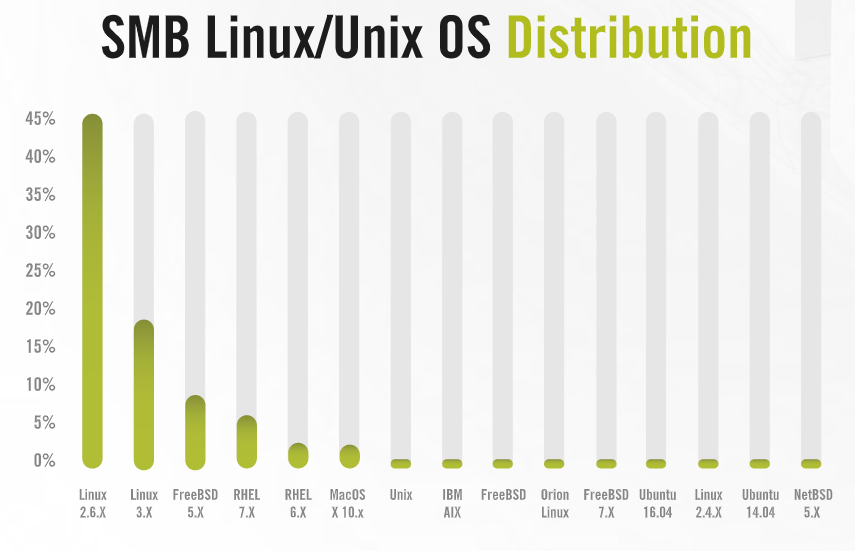
Almost half of all scanned Linux systems ran with an outdated kernel; more specifically, they had version 2.6 that has been out of support for the past three years and has upward of 65 known vulnerabilities.
This issue, though, is not as visible as deployed application systems, which hide the underlying OS distribution.
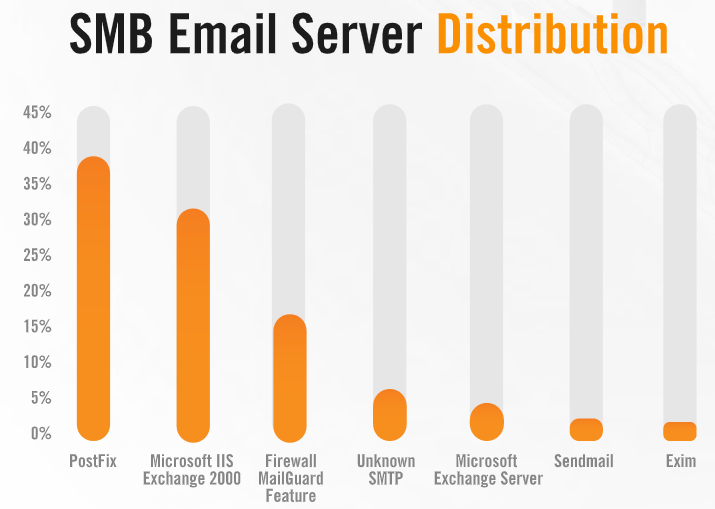
Another example of outdated software is the Exchange 2000 email server, accounting for close to a third of all email servers detected. The issue is that the product stopped receiving support in July 2010.
The most popular email server with the SMBs monitored by Alert Logic is PostFix, while Exim – the most widespread email server, falls in the last place.
Alert Logic says that the data was compiled from 5,000 attacks seen on a daily basis against its customer base over a period of six months, from November 2018 until April 2019.